Enterprise leaders are increasingly pushing AI initiatives into containerized environments to help them meet aggressive innovation goals. These workloads now run across public cloud clusters like AWS and Azure as well as private data centers using platforms like Red Hat OpenShift and Rancher, powering everything from customer-facing applications to internal AI models. But while deployment velocity has increased, security architecture has struggled to keep pace. Traditional security tools built to monitor traffic at the network perimeter typically lose visibility once traffic enters a Kubernetes environment. And that’s a big problem.
A lack of application-level visibility into your Kubernetes cluster can create significant risk for your business. Without insight into the traffic moving between your workloads, attackers can easily move threats laterally across clusters, sensitive data can leak through AI model interactions, and your teams may be left troubleshooting incidents without the context they need. Addressing this challenge requires you to focus on three core use cases of modern container security:
- Restoring application-layer visibility and control inside Kubernetes environments.
- Stopping lateral threat movement.
- Securing the generative AI development pipeline.
When these capabilities are in place, your team can innovate more quickly and without sacrificing security or resilience.
Restore Visibility and Control in the Kubernetes Black Box
Typically, legacy firewall solutions are unable to notice the traffic flowing between containers. This creates a risky environment where malicious activity and operational inefficiencies can hide in plain sight. When outages occur, the absence of clear visibility can lead to hours of finger-pointing between networking, security and DevOps teams while critical digital services remain offline. You can’t protect or repair what you can’t see (how many times have you read that lately?). Relying solely on basic cloud service provider (CSP) tools can result in unacceptably low threat detection and blocking rates.
Deep application-layer visibility into your container traffic changes this dynamic. By inspecting the actual "conversations" between services at Layer 7, security teams can manage multiple applications across the same cluster without compromising traffic identity. This context allows you to move beyond simple connectivity checks to enforce granular security policies based on what an application is actually doing. While this level of operational clarity can significantly reduce your mean time to resolution (MTTR) during an outage, its primary value is in ensuring your digital business remains available and resilient against sophisticated, application-specific threats.
Stop Lateral Threat Movement Across the Cluster
Traditional network security typically stops at the front door. Once a single container is compromised, your internal environments can become wide open for exploration because conventional tools lack visibility into advanced threats moving between workloads. Without strong internal controls, attackers can move laterally through your cluster, escalating access and searching for high-value targets. This absence of internal boundaries creates a significant economic risk for modern enterprises like yours. If an attacker gains a foothold in a noncritical web frontend, they should not have a clear path to your proprietary AI models, sensitive customer databases or other mission-critical assets.
PrismaⓇ AIRSTM enables a resilient architecture by tunneling container traffic directly to the firewall, effectively creating the "watertight bulkheads" needed for modern cloud environments. Just as a leak in one compartment shouldn't sink an entire ship, a breach in one workload shouldn't cascade across your infrastructure.
By centralizing container traffic, you gain the application-level visibility required to enforce precise L3/L4 microsegmentation policies alongside deep Layer 7 protection. This ensures that threats are contained at their point of origin, protecting your mission-critical assets and preventing a localized security incident from escalating into a brand-damaging data breach.
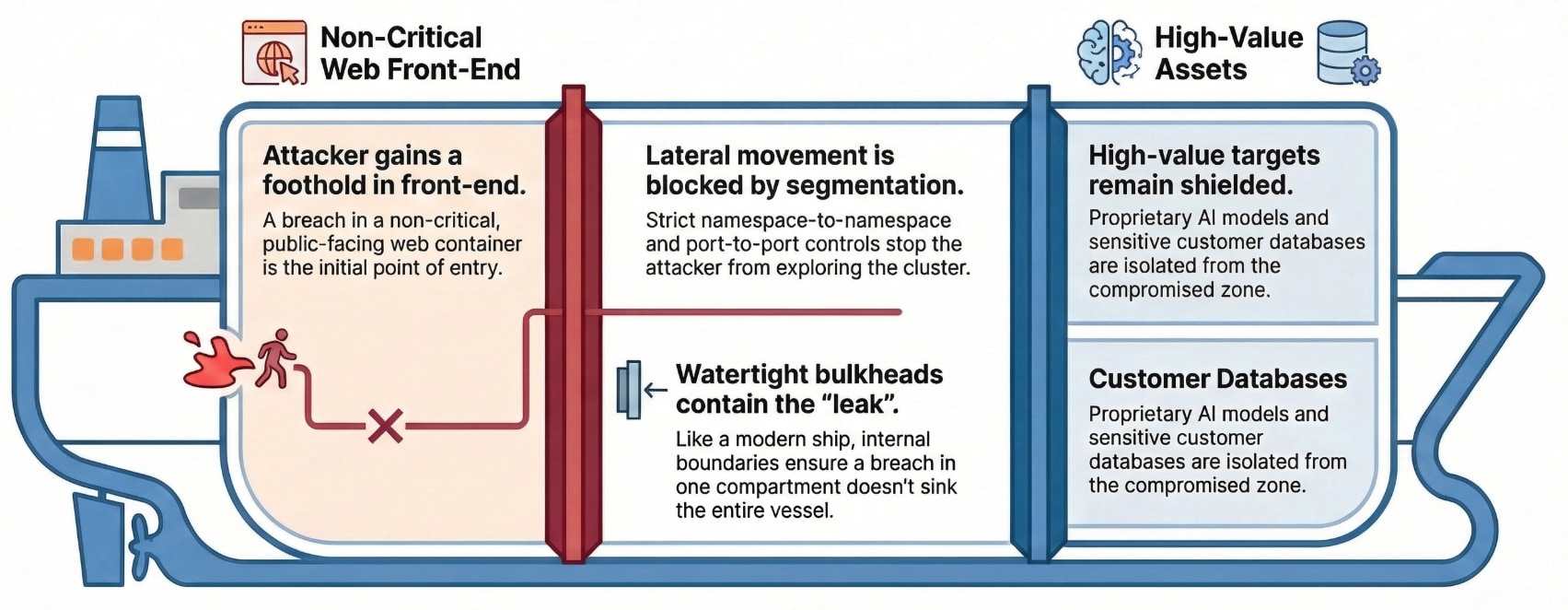
Just like watertight bulkheads on a ship, precise segmentation contains threats at their origin to prevent lateral movement and protect your mission-critical assets.
Secure the Enterprise Generative AI Pipeline
AI acceleration is a top priority for the C-suite, but unmanaged AI risks can quickly threaten your intellectual property. With the vast majority of AI workloads running in containers, an unsecured pipeline becomes a direct path for prompt injection, model denial-of-service and inadvertent data leakage. If your engineering team builds on a weak foundation, your AI innovations may end up collapsing under regulatory fines, security breaches or intellectual property theft.
Strategic leaders are addressing this by implementing targeted protections across the AI lifecycle, ensuring model interactions remain aligned with their corporate policy. Think of these protections as the specialized seals on a ship's fuel lines that prevent leakage of sensitive data into the public domain while ensuring that the engine of your AI innovation remains protected from external tampering.
While many vendors provide shift-left security controls to catch issues during development, AI applications still require robust runtime protection to defend against unpatched and unknown vulnerabilities once they are live. With the right safeguards in place, organizations are adopting AI with confidence rather than hesitation and are able to unlock innovation instead of restricting it.
Eliminate the Cloud Complexity Gap
Building a security model that actually works for your teams requires bridging the "cloud complexity gap.” The cloud complexity gap is the friction that occurs when high-velocity DevOps teams outpace the capabilities of traditional security operations. This gap stems from fragmented environments where virtual machines, containers and AI workloads are managed with different, often incompatible security tools, forcing teams to choose between development speed and protection. Trying to secure these silos individually is like trying to navigate a fleet of ships with different navigation systems; eventually, the lack of coordination leads to a collision.
Prisma AIRS helps bridge this gap by moving security outside the cluster and using CNI chaining to steer traffic for full Layer 7 inspection without disruptive in-cluster firewalls or complex configuration changes. This outside-in approach removes the friction that often slows high-velocity development environments. By consolidating security for virtual machines, containers and AI workloads into a single security stack, you gain a "unified bridge" from which to monitor and protect your entire digital fleet. This eliminates the management overhead and policy silos created by fragmented point solutions.
The goal here is to build lasting business resilience as you continue innovating with AI, not simply to add another security tool. Customers like Norlem already rely on Prisma AIRS to protect critical, fan-facing services where downtime or data exposure is unacceptable. With high-fidelity threat detection operating alongside modern development pipelines, security no longer needs to come at the expense of speed. So, instead of treating container security as a bottleneck, make it a foundation of your digital transformation.
Expose the Risks Hiding in Your Infrastructure
The first step to securing your container environment is recognizing what remains invisible to you. Many organizations assume their perimeter defenses provide sufficient protection, only to discover that internal traffic within their clusters is far more exposed than expected. These unseen gaps create potential pathways for attackers to move laterally, escalate privileges, or access sensitive data. Gaining visibility into these hidden attack paths is the difference between proactive resilience and reactive crisis management.
Request a complimentary Cloud Network and AI Risk Assessment (CLARA) to uncover where your container environments may lack critical Layer 7 protection. This targeted evaluation will help you identify potential attack paths through your clusters and highlight the areas where stronger controls are needed.