The increased volume and velocity of containerized development has allowed DevOps and development teams to react more quickly to user needs. However, the ephemeral nature of these environments creates additional challenges for security teams. Integrated tools and platforms are needed to ensure comprehensive security.
To meet those needs, we're proud to announce that Prisma Cloud from Palo Alto Networks has added support for Google Cloud Artifact Registry, the next generation container registry from Google Cloud.
Integrating with Google Cloud Artifact Registry
Today’s cloud native enterprises are leveraging the latest technologies to build and deploy applications more quickly and rapidly than ever before.
The State of Cloud Native Security 2020 survey revealed that 93% of organizations use multiple compute architectures for their cloud workloads, with containers and managed container services like Kubernetes accounting for nearly half of all workloads (45%). And the most recent survey from Cloud Native Computing Foundation (CNCF) showed that 27% of teams perform daily release cycles, up from 15% in 2018. And 28% release monthly, an increase from 20% in 2018.
Google Cloud’s Artifact Registry allows these fast-moving cloud native organizations to manage container images as well as language and OS packages from a single location.
This integration builds on other documented Google Cloud integrations with both Prisma Cloud and additional Palo Alto Networks portfolio offerings. Prisma Cloud also supports key Google Cloud integrations and technologies, such as:
- Google Cloud Build for continuous integration and continuous delivery
- Google Compute Engine and Google Kubernetes Engine (GKE) to protect cloud VMs and containerized applications at runtime
- Google Cloud Security Command Center to centralize visibility into security and compliance risks associated with cloud assets on Google Cloud.
Securing Containers Across the Application Lifecycle
To fully secure containerized applications, organizations need to ensure they have embraced a full lifecycle approach for prioritizing risk, managing compliance issues and protecting applications at runtime. Prisma Cloud allows organizations to apply this approach to their cloud native applications on Google Cloud.
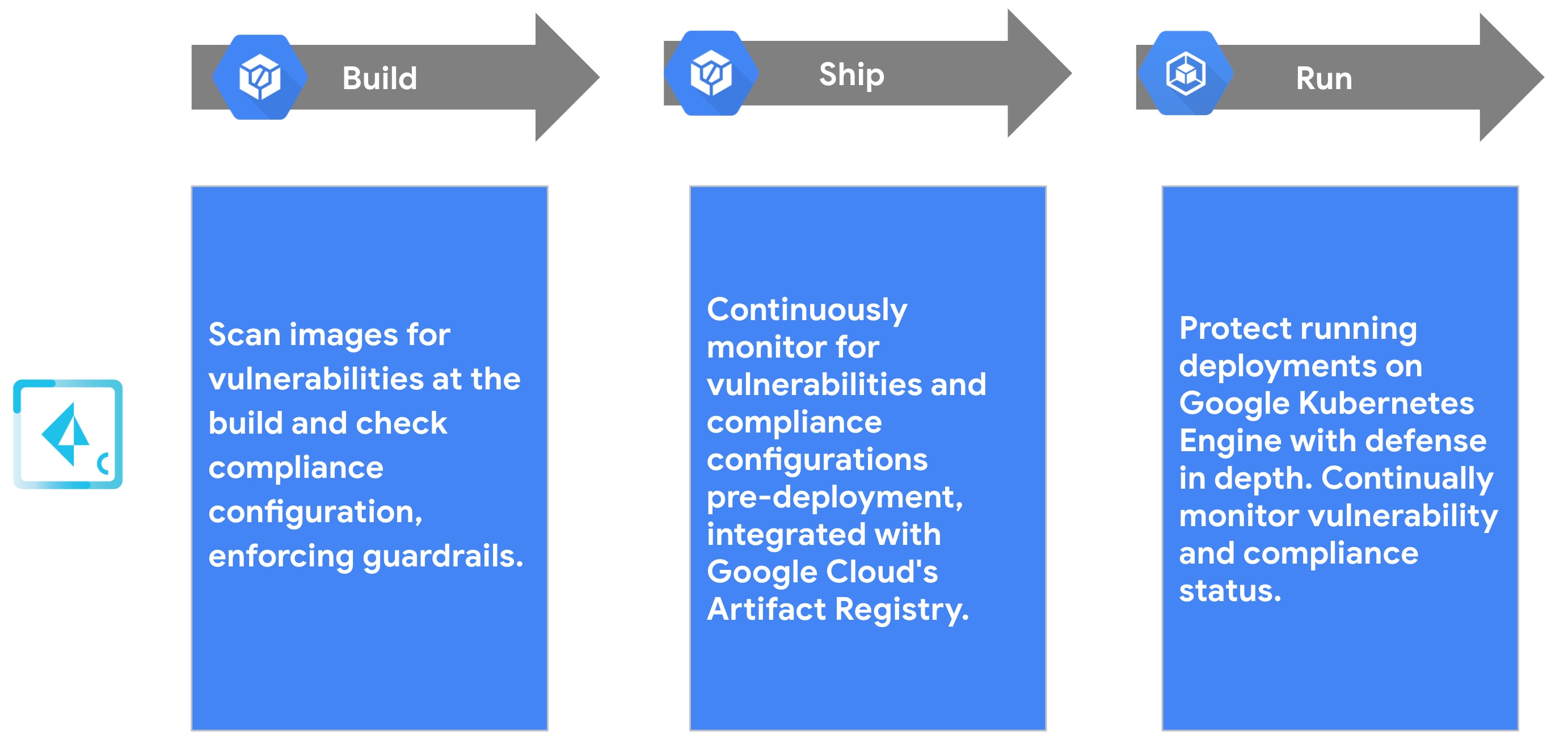
Build
During the build stage, Prisma Cloud scans infrastructure-as-code (IaC) templates for misconfigurations, with integrations for software configuration managers (SCM), integrated development environments (IDE), and continuous integration (CI) tools. Additionally, users can scan container images as part of their automated workflows with Google Cloud Build, with the ability to enforce application policies based on vulnerability severity or internal policy compliance.
Deploy
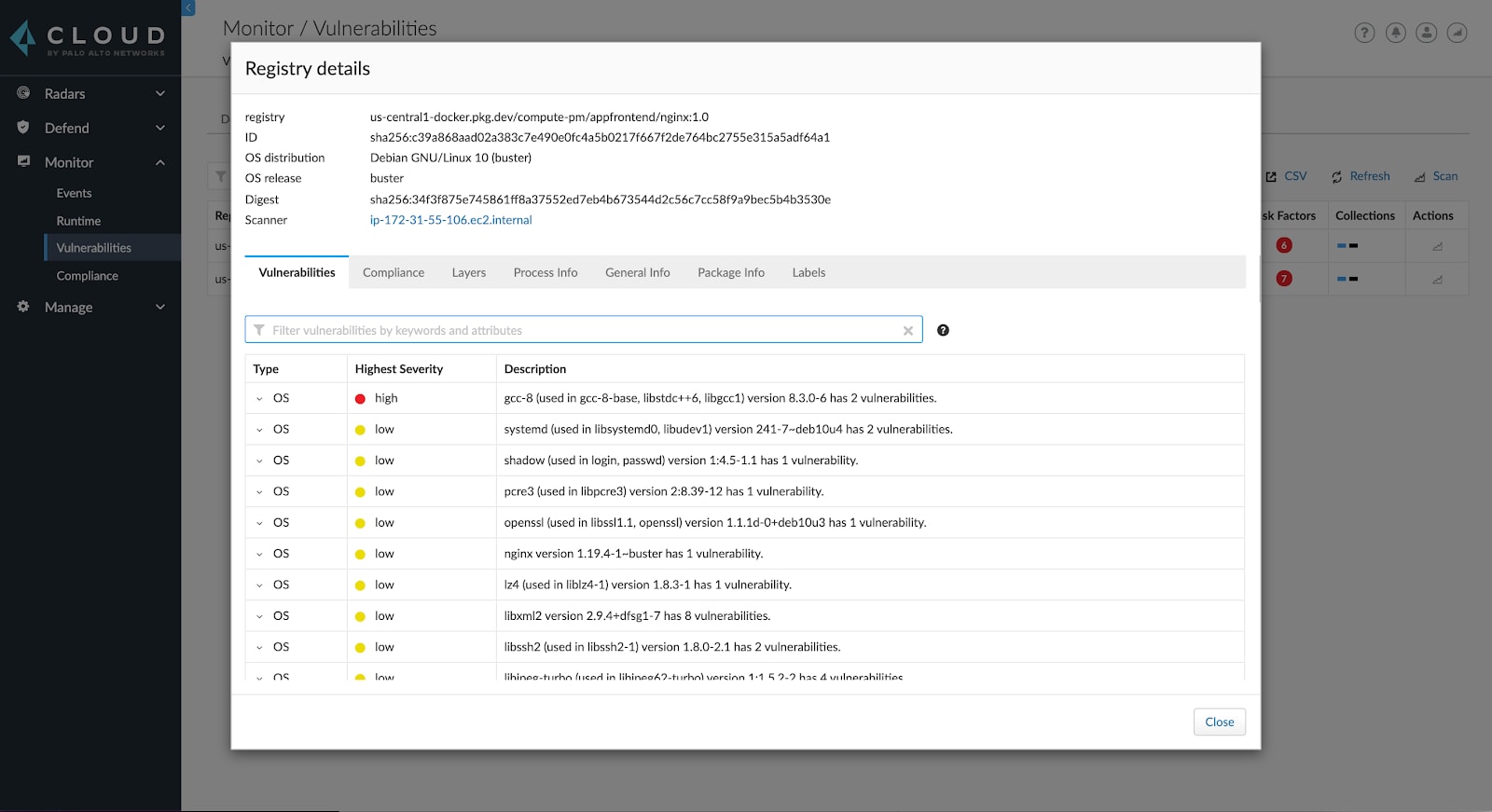
At the deploy phase, Prisma Cloud continuously monitors container registries such as Google Cloud's Artifact Registry to provide uninterrupted visibility and control over risk and compliance status. Users can set granular rules governing image trust to ensure that deployments always originate from trusted images sourced in Google Cloud's Artifact Registry.
Run
At runtime Prisma Cloud continuously monitors all resources on specified Google Cloud accounts. Dashboards display vulnerability and policy compliance status for applications, so organizations can easily audit and improve security posture. For cloud native applications running on GKE, Prisma Cloud automatically models normal application behavior, allowing it to alert on or help prevent unexpected and unwanted activity. Should any anomalous or nefarious activity occur, it can surface vital audit and forensic data along with the prevention controls that were governing the activity.
Begin using Prisma Cloud for Google Cloud's Artifact Registry
To learn more about Prisma Cloud on Google Cloud, visit the Prisma Cloud GCP Marketplace listing or the Palo Alto Networks partnership page.