As enterprises have moved their data assets to the cloud, they depend on SaaS applications to conduct their business. Today, SaaS apps have evolved to become highly customizable, increasing the risk of misconfigurations that can result in a data breach or data exposure to the public internet.
Companies must harden their SaaS app security posture to help avoid a potential breach and protect sensitive data stored in these applications.
An example of what happens when an organization doesn’t maintain a strong SaaS app security posture was recently in the news. ServiceNow, a platform widely used by businesses for IT service management, announced a potential misconfiguration issue that could result in unintended access and potential data leaks within their platform.
A Real-Life Example: Weak SaaS App Security Posture
ServiceNow recently announced on its support site that misconfigurations within its platform could result in "unintended access" to sensitive data. This security exposure is a critical concern that could have resulted in significant data leakage of sensitive corporate data to the public.
ServiceNow detailed this issue in their knowledge base as a potential misconfiguration due to an Access Control List (ACL) with an empty check for Roles, Conditions and Script which are part of the ACL. This potential misconfiguration allowed the widget defined as “public” to result in the underlying resource being accessible to any user, including a guest user through that widget.
The issue stems from a widget known as SimpleList that can be used to organize information from multiple sources to display records into easily readable tables. Service portal widgets that are active and set to “public” rely on the underlying ACL system to protect sensitive data.
The default configuration for the SimpleList widget and the default setting of “Public Access” to the tables have allowed the data in the tables to be accessed remotely by unauthenticated users. These tables can include sensitive data, including personal information, patient information, and employee details.
Although ServiceNow recommended remediation steps to address this concern in the same knowledge base article, this incident should serve as a wake-up call for enterprises. This situation emphasizes how important it is for organizations to seriously consider a solution that can detect configurations that deviate from the security best practices so they can remediate these misconfigurations before they pose any danger to SaaS app data.
How SSPM Can Help
SaaS Security Posture Management (SSPM), natively integrated into Prisma Access and Next-Generation CASB, helps detect and remediate misconfigured settings in sanctioned SaaS applications. SSPM provides:
- Continuous monitoring that scans security-related settings for 90+ SaaS applications.
- Misconfiguration detection that finds dangerous misconfigurations using built-in best practices, categorizing misconfigurations by severity to help you prioritize risks.
- Reduced deployment time by automatically organizing settings into policies for normalization and prioritization via easy-to-understand language.
- Comprehensive and effortless remediation via misconfiguration alerts to help remediate issues quickly across applications with a single click or guided instructions.
- Best practices recommendations through scans that identify settings that have the potential to leave your organization less secure or create risks.
- Risky account identification finds accounts that are not connected to your IdP but are locally configured.
- Drift prevention enables configuration locking so that a setting does not become a misconfiguration in the future.
- Ticketing system integration with systems such as Jira to export findings and track changes.
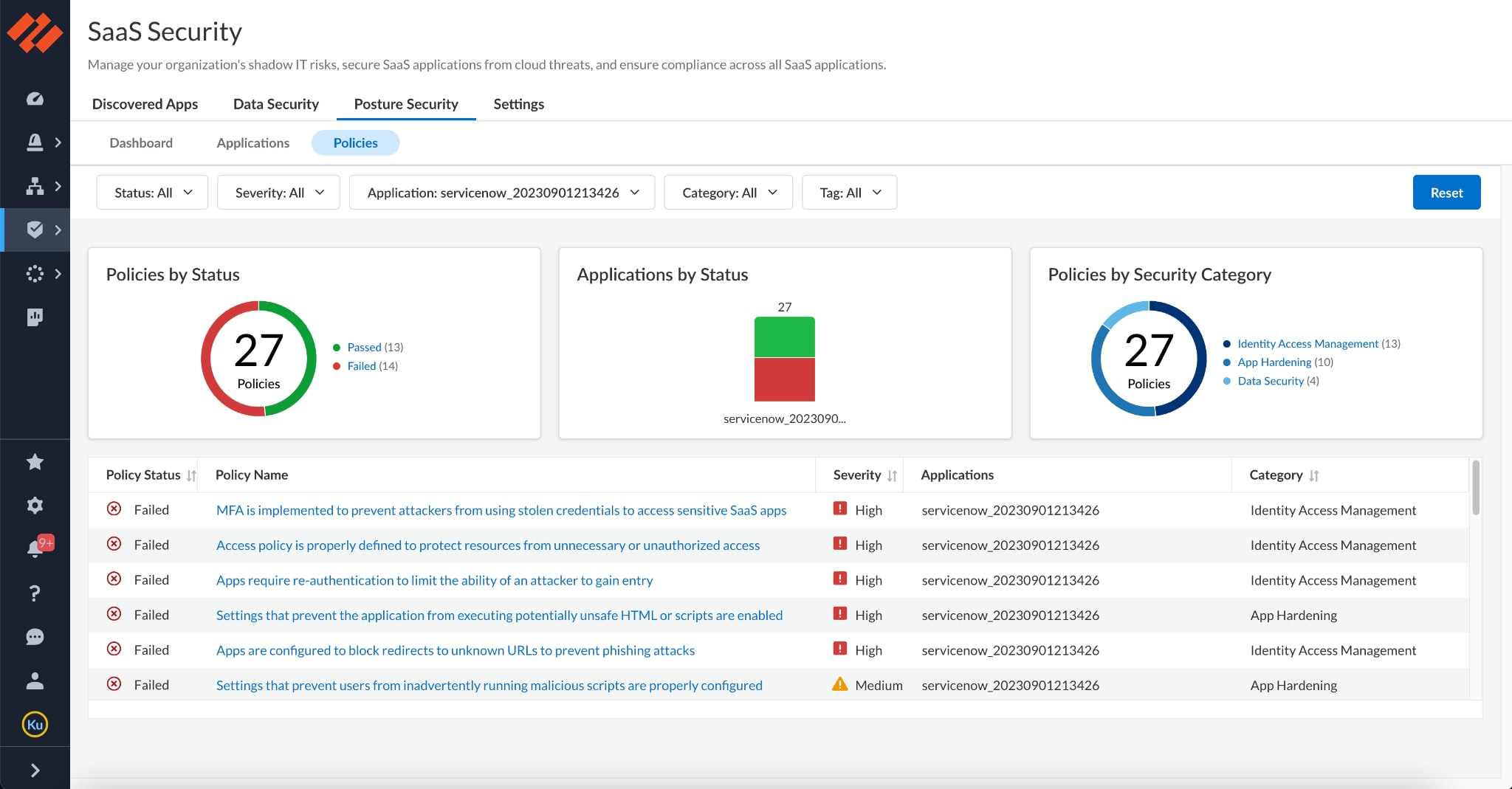
Figure 1. Sample view of Palo Alto Networks SSPM detecting misconfigurations within ServiceNow application.
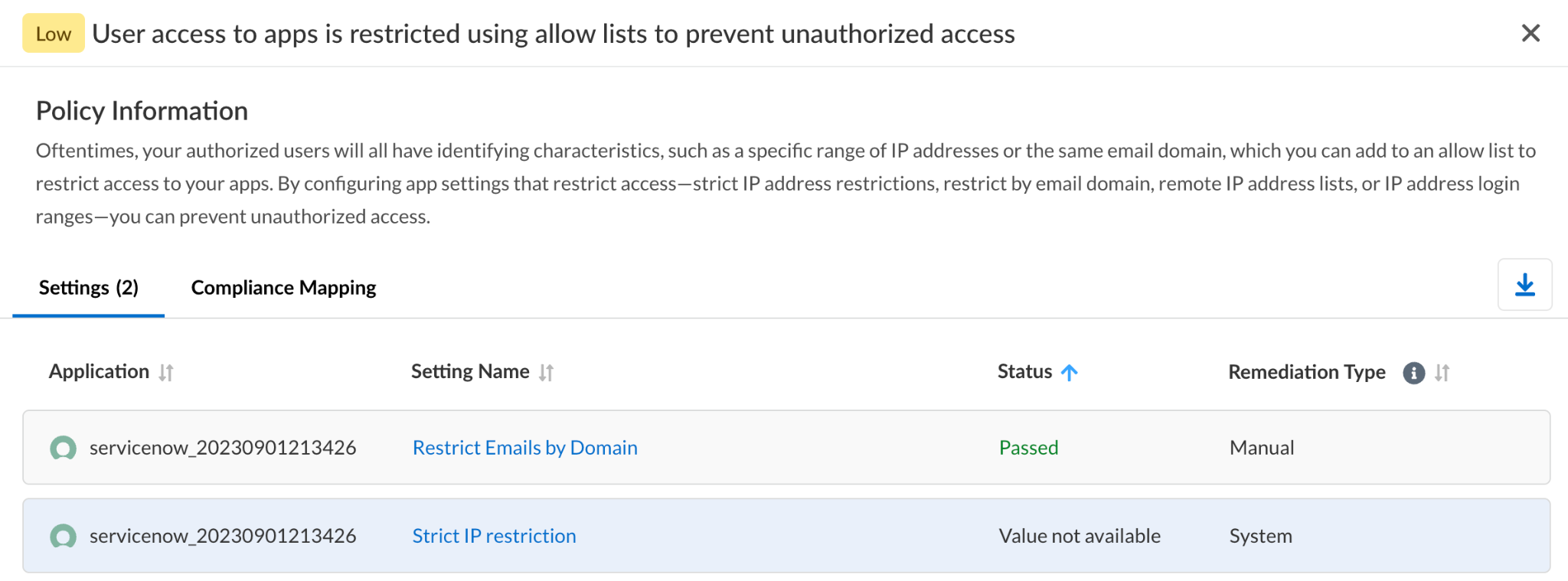
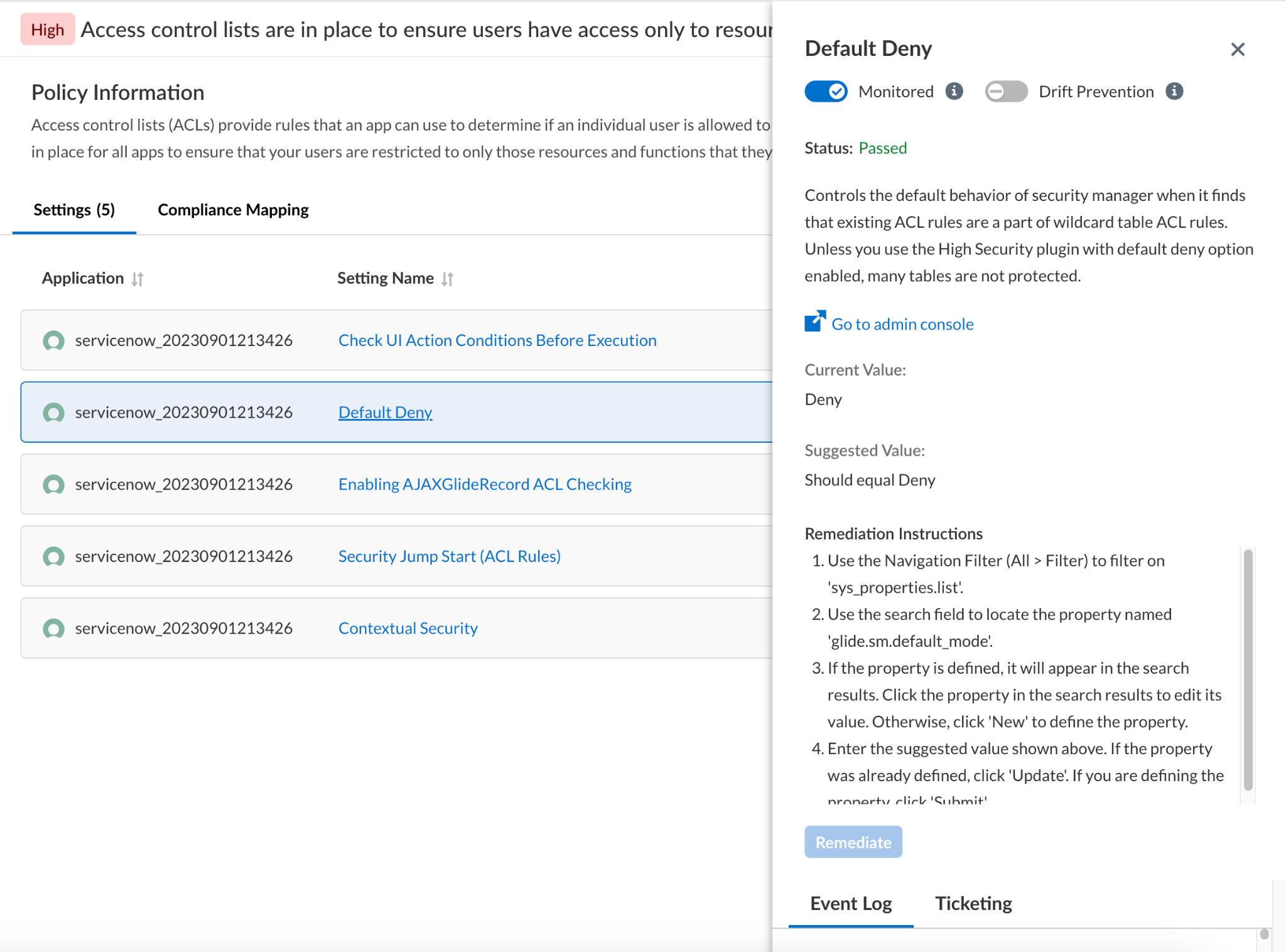
Figure 2. Sample view of settings relevant to controlling user access to apps, single click remediation option, and drift prevention.
Protect Yourself from SaaS App Misconfiguration with SSPM
ServiceNow’s misconfiguration warning is a wake-up call for organizations to be vigilant and proactive in monitoring their SaaS applications’ posture with an SSPM solution that detects misconfigurations with continuous and comprehensive monitoring, alerting, and remediation capabilities.
The Palo Alto Networks SSPM continuously monitors the posture of SaaS apps and alerts whenever a security setting deviates from best practices, ensuring the SaaS app is hardened against misconfigurations. Interested in learning more? Reach out for a demo.