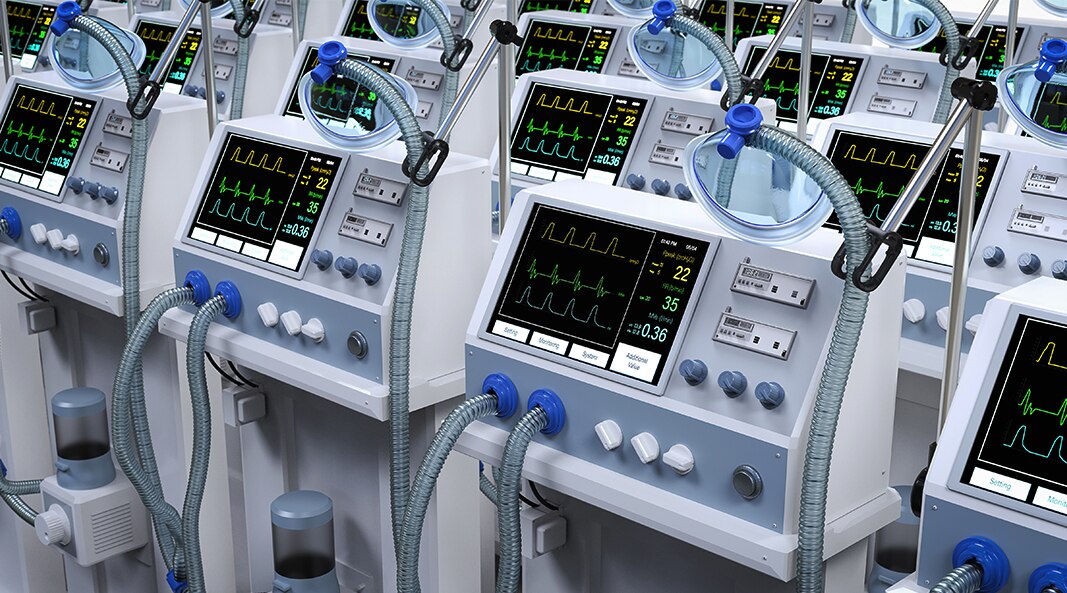
Medical IoT Security, the most comprehensive Zero Trust solution for medical devices

Complete device visibility with ML-based discovery
Medical IoT Security enables healthcare organizations to accurately identify and classify all connected devices in their network, including those never seen before.
Combines Palo Alto Networks App-IDTM technology and deep packet inspection (DPI) for accuracy with a patented three-tiered machine learning (ML) model for speed in device profiling.
Use profiles to classify any connected medical device to reveal its type, vendor, model and more than 50 unique attributes, including firmware, OS, serial number, MAC address, physical location, subnet, access point, port usage, and applications.
Bypass the limitations of signature-based solutions in new device discovery using cloud scale to compare device usage, eliminate soak time, validate profiles and fine-tune models to manage all devices.

Prioritize risk with continuous vulnerability assessments
Medical IoT Security helps healthcare organizations find all the information they need to quickly evaluate vulnerable devices, assess compliance and initiate the next steps.
Unites disparate solutions from traditional IT security technology into one, simplifying and automating analysis and assessment for security teams.
Uses ML to generate device profiles from five key behaviors – internal connections, internet connections, protocols, applications and payloads – then compares them over time against similar crowdsourced devices.
Continuously evaluates and adjusts for risk by assessing Manufacturer Disclosure Statement for Medical Device Safety (MDS2) security information, such as antivirus capabilities, ePHI, device vendor patching information, Unit 42® threat intelligence, third-party vulnerability management systems, Software Bill of Materials (SBOM) mapping and Common Vulnerabilities and Exposures (CVEs) data.
Generates risk scores based on the Common Vulnerability Scoring System (CVSS), providing an effective way to prioritize results.
Quickly exposes any behavioral anomalies and threat details for security teams to initiate a response and consistently reduce the attack surface area.
Segment devices and enforce least privilege access policies
Medical IoT Security lets healthcare organizations implement security best practices with context-aware segmentation to restrict lateral movement between connected medical devices.
Provides risk-based policy recommendations to control connected medical device communication.
Segments connect medical devices and apply Zero Trust policies through NGFW or NAC.
Uses our patented Device-ID™ policy construct to share device profile information and ensures that control placed on an individual device is consistent regardless of network location.
Reduces your attack surface by providing context to segment connected medical devices into different VLANs and applying the Zero Trust methodology.

Prevent known and unknown threats
Medical IoT Security stops all threats to your connected medical devices with the industry’s leading IPS, malware analysis, web and DNS prevention technology.
Coordinate intelligence to prevent all connected clinical device threats without increasing workloads for your security personnel because of seamless integration with Medical IoT Security and our Cloud-Delivered Security Services.
Decrease response times with our ML-Powered NGFWs that can dynamically isolate connected medical devices with validated threats upon detection, giving your security team time to form remediation plans without the risk of further infection from that device.
Enhance SOC and SIEM context for alert triage, investigation and threat response with complete visibility, context and actionable insights.

Simplify operations and get device utilization insights
Medical IoT Security alleviates the pain of capital planning and preventive maintenance while saving costs on patient care by automatically tracking and reporting on connected medical device usage and resource allocation.
Gain operational insights, including connected medical device operating hours, scan type insights, patient experience, average use, vendor remote maintenance activity and side-by-side comparisons of connected clinical devices.
Generate reports to plan and implement efficient capital planning and business operations optimization.
Utilize full device context information across your security operations for context-aware segmentation, policies and incident response.
Automatically track and visualize connected medical device usage, location and more across sites and easily generate reports.
Identify and secure all connected medical devices and other IoT and IT devices mapped to the HIPAA framework.
Need more proof points?
Request Your Medical IoT Security Demo
See what the most comprehensive Zero Trust security solution for medical devices can do for your organization.
